ALLOCATION OF THE STACK:
Allocation of the stack requires memory. The memory will be managed by the kernel. So, if you are writing the runtime to allocate the memory, does that runtime code call the kernel functions????
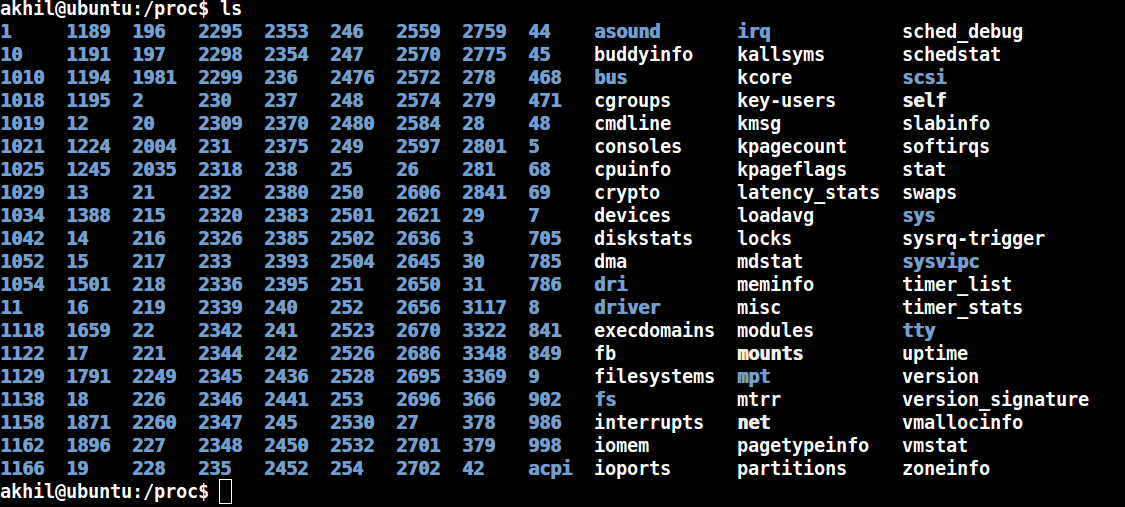
YES!!!! It will have to interact with the kernel functions. The kernel will be notified through some interface that the process is requesting the memory for memory for execution. Now think about this... "If you are writing a code that interacts with the Linux Kernel, will this code work on windows???" .
The code which interacts with the Linux kernel's functions are specific to Linux and cannot work on Windows as the functions will be significantly different on both the kernels. The kernel is different for Windows and Linux and hence the runtime code which interacts with the kernel of the operating system should be specific to the OS. This means that runtime code is Operating System specific. Even the linker is OS specific. What ever the linker does, that process is called as the built process. This built process Operating System specific. This is the reason why -exe files which are compiled in the Linux platform does not work on Windows and vice-versa. If we compile and built for one platform, it wont work for the other platform because of the presence of the runtime.
Presence of the runtime binds an executable to a specific Operating System. Here if a requirement where we need to compile and built a program which is compatible on Windows and Linux, then we need to build an executable image without the runtime code. Now, the runtime code is necessary for the code to get initialized and without the runtime the code will not run. Now, how do we solve this issue?????
We will remove runtime and make it a software. If we take out the runtime out of the executable and make it a software, then the exe wont contain the runtime. The benefit of this is a single runtime can be shares by the multiple exe's. Virtual Machine of Java is somewhat similar to this concept. All the executables will run directly on that particular virtual machine. With this the executable is independent of the runtime. The benefit with this is we can run the executable in any platform we require which is specific to the OS. Java Virtual Machine is specific to window, JVM is specific to Linux but not the Java code.
In this way we can make the executable independent of the platform by making the runtime code a library. This runtime code will initialize the stack.
Now what is mean by a library?
How is library going to bind to an executable?
How many types of libraries are there?
We will learn about the libraries in our next article.......................
YES!!!! It will have to interact with the kernel functions. The kernel will be notified through some interface that the process is requesting the memory for memory for execution. Now think about this... "If you are writing a code that interacts with the Linux Kernel, will this code work on windows???" .
The code which interacts with the Linux kernel's functions are specific to Linux and cannot work on Windows as the functions will be significantly different on both the kernels. The kernel is different for Windows and Linux and hence the runtime code which interacts with the kernel of the operating system should be specific to the OS. This means that runtime code is Operating System specific. Even the linker is OS specific. What ever the linker does, that process is called as the built process. This built process Operating System specific. This is the reason why -exe files which are compiled in the Linux platform does not work on Windows and vice-versa. If we compile and built for one platform, it wont work for the other platform because of the presence of the runtime.
Presence of the runtime binds an executable to a specific Operating System. Here if a requirement where we need to compile and built a program which is compatible on Windows and Linux, then we need to build an executable image without the runtime code. Now, the runtime code is necessary for the code to get initialized and without the runtime the code will not run. Now, how do we solve this issue?????
We will remove runtime and make it a software. If we take out the runtime out of the executable and make it a software, then the exe wont contain the runtime. The benefit of this is a single runtime can be shares by the multiple exe's. Virtual Machine of Java is somewhat similar to this concept. All the executables will run directly on that particular virtual machine. With this the executable is independent of the runtime. The benefit with this is we can run the executable in any platform we require which is specific to the OS. Java Virtual Machine is specific to window, JVM is specific to Linux but not the Java code.
In this way we can make the executable independent of the platform by making the runtime code a library. This runtime code will initialize the stack.
Now what is mean by a library?
How is library going to bind to an executable?
How many types of libraries are there?
We will learn about the libraries in our next article.......................